Module 3: Use security alerts and leverage dynamic packet capture
Estimated time: 20 min
Learning objectives
- Use global alerts to notify security and operations teams about unsanctioned or suspicious activity.
- Configure packet capture for specific pods to capture packet payload for further forensic analysis and explore the captured payload.
Use security alerts
We deployed security alerts in the first module. While we were implementing the use cases, some of them have triggered the alerts and now we can explore them.
-
Review alerts manifests.
Navigate to
demo/50-alertspath and review YAML manifests that represent alerts definitions. Each file containes an alert template and alert definition. Alerts templates can be used to quickly create an alert definition in the UI. -
View triggered alerts.
Open
Alertsview to see all triggered alerts in the cluster. Review the generated alerts.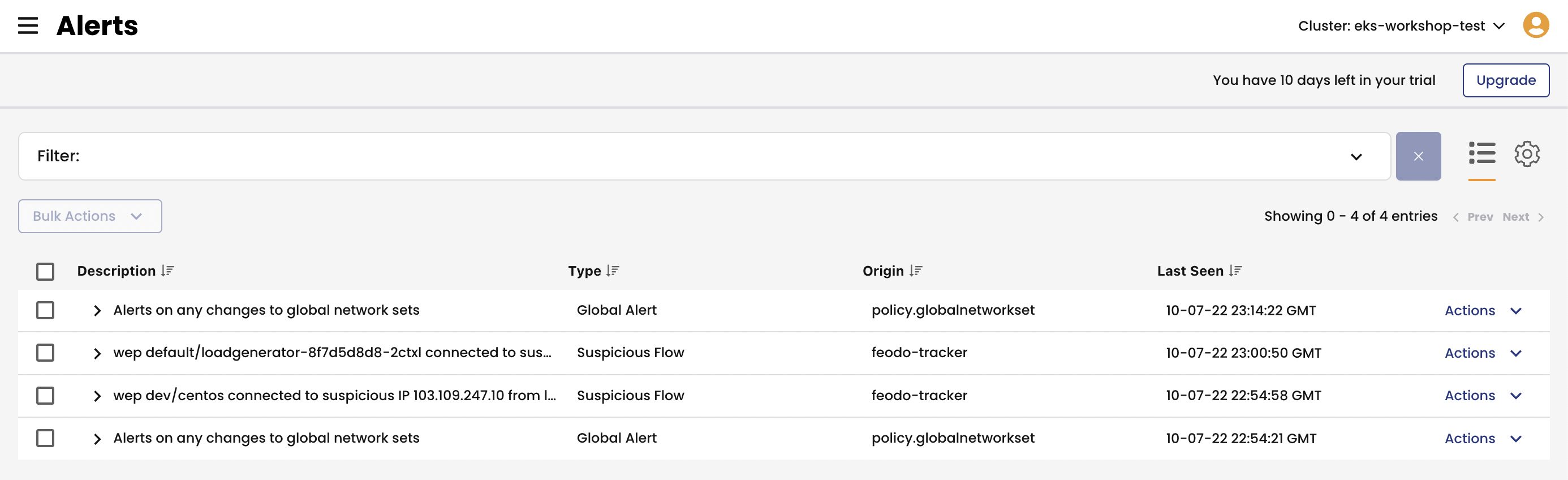
You can also review the alerts configuration and templates by navigating to alerts configuration in the top right corner.
Leverage dynamic packet capture
Refer to packet capture documentation for more details about this capability.
-
Configure packet capture.
Navigate to
demo/60-packet-captureand review YAML manifests that represent packet capture definition. Each packet capture is configured by deploing aPacketCaptureresource that targets endpoints usingselectorandlabels.Deploy packet capture definition to capture packets for
dev/nginxpods.kubectl apply -f demo/60-packet-capture/nginx-pcap.yamlOnce the
PacketCaptureresource is deployed, Calico starts capturing packets for all endpoints configured in theselectorfield.Stop packet capture by removing the
PacketCaptureresource.kubectl delete -f demo/60-packet-capture/nginx-pcap.yaml -
Install
calicoctlCLIThe easiest way to retrieve captured
*.pcapfiles is to use calicoctl CLI.# download and configure calicoctl curl -o calicoctl -O -L https://docs.tigera.io/download/binaries/v3.7.0/calicoctl chmod +x calicoctl sudo mv calicoctl /usr/local/bin/ calicoctl version -
Fetch and review captured payload.
The captured
*.pcapfiles are stored on the hosts where pods are running at the time thePacketCaptureresource is active.Retrieve captured
*.pcapfiles and review the content.# get pcap files calicoctl captured-packets copy dev-capture-nginx --namespace dev ls dev-nginx* # view *.pcap content tcpdump -Ar $(ls dev-* | head -1) tcpdump -Xr $(ls dev-* | head -1)